Cyber operations have played a central role in US-Israeli activities involving Iran, while Tehran has responded with its own cyber campaigns targeting perceived adversaries. Analysts suggest that a highly precise operation—such as a potential strike on Iran’s Supreme Leader—would be nearly impossible without overwhelming cyber and intelligence dominance.
At the same time, European security officials warn that these capabilities, which Iran also possesses, could trigger immediate repercussions beyond the battlefield, particularly in the form of cyber attacks affecting European Union nations.
As the conflict entered its tenth day, Iran experienced a near-total internet blackout. Data from NetBlocks indicated that national connectivity had dropped to roughly 1% of its normal level. During this period, Iran faced multiple hostile cyber activities, including the hacking of its BadeSaba religious calendar application.
Despite the disruption, Iran has also been actively conducting cyber operations. Security firm Check Point Software reported a surge in attacks targeting internet-connected cameras from two manufacturers beginning on February 28. The activity reportedly originated from infrastructure linked to Iranian threat actors. The company also noted increased exploitation attempts against Qatar, Bahrain, Kuwait, the United Arab Emirates, and Cyprus as the conflict intensified.
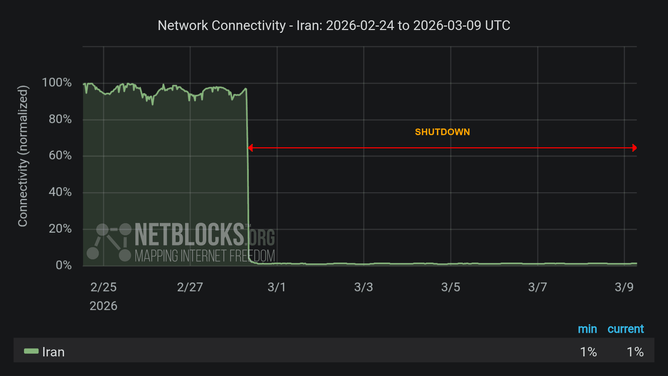
Internet activity in Iran is below 1% as the country suffers near total blackout | Credit: NetBlocks
Cyber warfront
The initial phase of US and Israeli strikes reportedly included coordinated cyber actions designed to disrupt communications in key areas of Tehran. Mobile towers around Pasteur Street—an area housing major government institutions—were targeted to interfere with warning systems during the strikes.
Intelligence gathering also relied heavily on compromised surveillance systems. Reports indicate that many traffic cameras in Tehran had been infiltrated years earlier, with their encrypted video feeds transmitted to servers outside Iran. Analysts say such access would provide valuable real-time intelligence during military operations.
In addition, advanced algorithms reportedly allow Israeli intelligence services to automate the once labor-intensive process of tracking high-priority individuals.
Israel targets cyberwarfare headquarters
According to the Israel Defense Forces, an early-March strike targeted a large military compound in eastern Tehran. The facility allegedly housed the cyber warfare headquarters of the Islamic Revolutionary Guard Corps, along with elements of its intelligence directorate.
While the full extent of the damage to Iran’s digital capabilities remains uncertain, cybersecurity researchers report that Iranian-linked cyber activity across the region has continued despite infrastructure damage and widespread internet disruptions within the country.
Researchers from Palo Alto Networks’ Unit 42 observed a growing wave of activity from pro-Iranian hacktivist groups. Analysts note that while Iran’s internet outages may temporarily limit sophisticated state-level cyber operations, opportunistic attacks are still likely to continue.
By early March, dozens of pro-Iranian hacktivist groups were active online, claiming disruptive attacks against Israeli and regional targets.
One of the most prominent actors is a persona known as Handala Hack, believed to have links to Iran’s Ministry of Intelligence and Security. The group has claimed responsibility for cyber breaches affecting an Israeli energy exploration company, Jordanian fuel infrastructure, and attempted intrusions into Israeli healthcare networks shortly before the physical conflict began.
Other groups—including Cyber Islamic Resistance, Dark Storm Team, and the Fatimiyoun Cyber Team—have coordinated distributed denial-of-service attacks, data-wiping campaigns, and website defacements targeting government agencies, financial institutions, and infrastructure across the Middle East.
Some actors have also claimed access to industrial control systems and drone-defense technologies.
These activities illustrate how Iran’s cyber ecosystem combines state interests with loosely connected activist networks that amplify disruption and political messaging.
Tactics shaping Iran’s cyber operations
Iranian cyber campaigns often blend espionage with disruptive tactics designed to pressure adversaries. Researchers have documented operations involving phishing campaigns, credential harvesting, destructive malware, and strategic data leaks.
In one recent case, attackers distributed a malicious Android version of Israel’s RedAlert emergency warning application. The fake app was used to collect surveillance data and extract sensitive information from infected devices.
More broadly, Iran-aligned groups frequently exploit unpatched software vulnerabilities, conduct targeted spear-phishing operations, and deploy “hack-and-leak” strategies intended to embarrass political opponents or influence public opinion.
Security analysts say these tactics are designed not only to disrupt infrastructure but also to create psychological pressure during times of geopolitical tension.
A fragmented but persistent cyber capability
The reported strike on Iran’s cyber headquarters highlights how modern conflicts increasingly combine cyber operations with traditional military force.
However, experts caution that destroying a single physical facility is unlikely to significantly weaken Iran’s cyber capabilities. The country’s cyber infrastructure relies on distributed networks of operators, pre-positioned malware, and proxy actors operating across multiple locations.
As a result, analysts believe the digital dimension of the conflict will likely continue even if the immediate military confrontation subsides.
For governments and organizations across the Middle East and potentially beyond, the cyber battlefield may remain active long after the physical fighting ends.
Source: CyberMagazine Edited by Bernie